PCB Design for Security: How to Implement Secure Communication and Authentication
PCB Design for Security: How to Implement Secure Communication and Authentication
Effective PCB design is crucial for ensuring the security of communication and authentication protocols in modern electronic systems. With the increasing demand for secure transactions and data exchange, securing the communication and authentication processes is essential for protecting sensitive information.
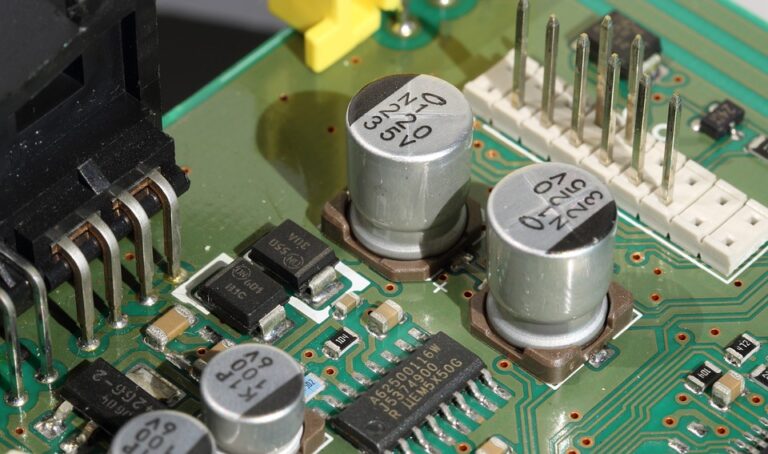
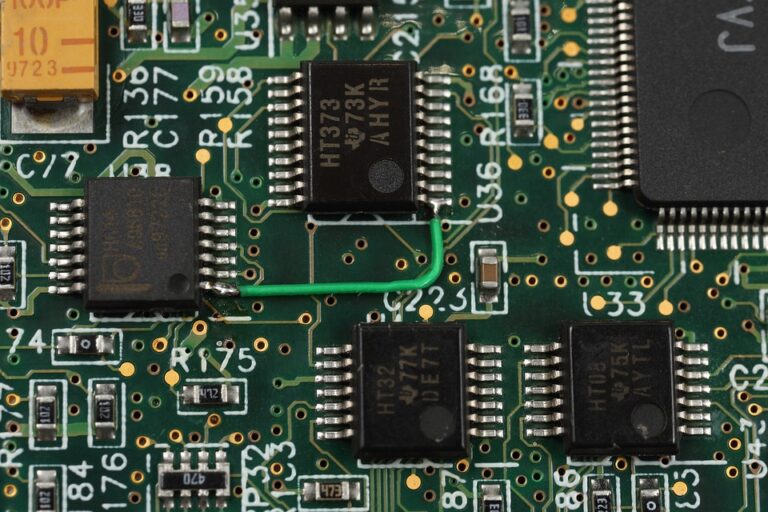
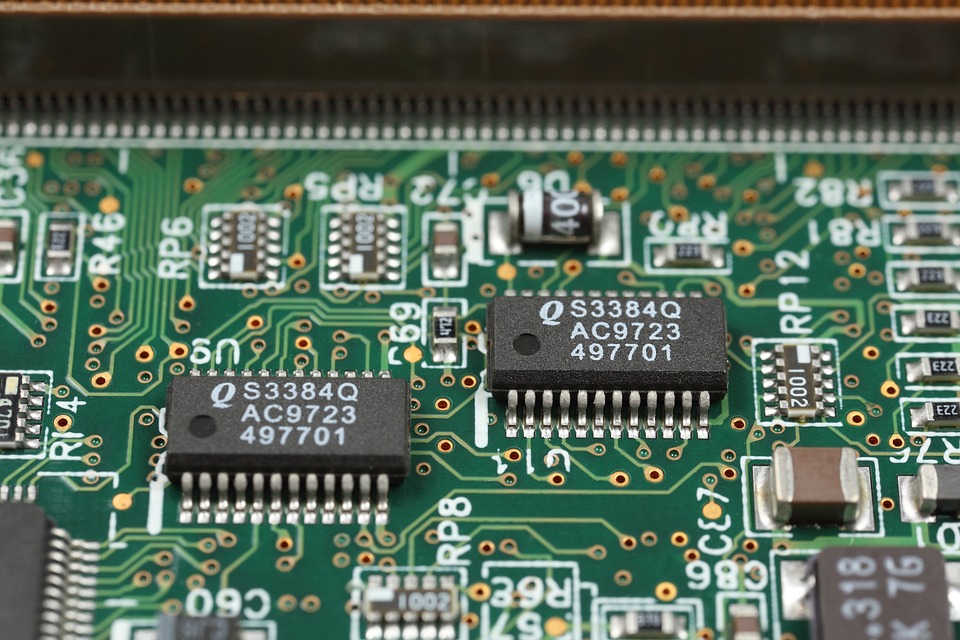
PCB (Printed Circuit Board) design plays a significant role in the development of secure communication and authentication systems. A well-designed PCB can provide robust security for the entire system, ensuring the integrity and confidentiality of data transmitted and stored. In this article, we will discuss the importance of PCB design for security and how to implement secure communication and authentication protocols in the design process.
Why is PCB Design Important for Security?
PCB design influences the overall security of an electronic system. A well-designed PCB ensures that the various components, such as sensors, actuators, and control units, are properly interfaced and isolated, reducing the risk of malicious attempts to access or disrupt the system.
Here are some reasons why PCB design is critical for security:
- Electromagnetic Interference (EMI): A well-designed PCB can minimize EMI, which can compromise the security of sensitive electronic components.
- Data Integrity: A PCB design that ensures secure data storage and transmission can prevent data tampering and unauthorized access.
- Cybersecurity: A robust PCB design can provide an additional layer of security against cyber threats, such as State-of-the-Art (SoTA) attacks.
Implementation of Secure Communication and Authentication Protocols in PCB Design
Implementing secure communication and authentication protocols in PCB design involves several steps:
- Secure Authentication Protocols: Implement secure authentication protocols, such as SSL/TLS, when transmitting sensitive data over the network. This ensures that only authorized devices or systems can access the data.
- Data Encryption: Encrypt data both in-transit and at-rest to prevent eavesdropping, tampering, and unauthorized access.
- Secure Boot Process: Implement a secure boot process that ensures the authenticity of the Bootloader and the operating system, preventing malware injection and tampering.
- Secure Communication Protocols: Implement secure communication protocols, such as HTTPS, when transmitting sensitive data over the network.
- Firmware Protection: Implement secure firmware loading and verification mechanisms to prevent malware injection and tampering.
Best Practices for Secure PCB Design
Here are some best practices to consider when designing a secure PCB:
- Use a Secure Boot Process: Implement a secure boot process that ensures the authenticity of the Bootloader and the operating system.
- Encrypt Sensitive Data: Encrypt sensitive data both in-transit and at-rest to prevent eavesdropping, tampering, and unauthorized access.
- Implement Secure Communication Protocols: Implement secure communication protocols, such as HTTPS, when transmitting sensitive data over the network.
- Use Secure Authentication Protocols: Implement secure authentication protocols, such as SSL/TLS, when authenticating devices or systems.
- Verify Firmware Authenticity: Verify firmware authenticity during the boot process to prevent malware injection and tampering.
Conclusion
Effective PCB design is crucial for ensuring the security of communication and authentication protocols in modern electronic systems. By implementing secure communication and authentication protocols, such as secure boot processes, data encryption, and secure authentication, PCB designers can ensure the integrity and confidentiality of sensitive information. Moreover, adhering to best practices, such as encrypting sensitive data, implementing secure communication protocols, and verifying firmware authenticity, can help to reduce the risk of security breaches and vulnerabilities.
FAQs
Q: What is the primary purpose of PCB design for security?
A: The primary purpose of PCB design for security is to ensure the integrity and confidentiality of sensitive information by implementing secure communication and authentication protocols.
Q: What is the difference between secure authentication and secure communication protocols?
A: Secure authentication protocols ensure that only authorized devices or systems can access the system, while secure communication protocols ensure that data transmitted over the network is encrypted and tamper-proof.
Q: How can I ensure the authenticity of firmware in my PCB design?
A: You can ensure the authenticity of firmware by verifying its digital signature during the boot process and implementing secure firmware loading and verification mechanisms.
Q: What are some common security threats to electronic systems?
A: Some common security threats to electronic systems include EMI, data tampering, and cyber attacks, which can compromise the security and integrity of sensitive information.